.png)
APIs don't disappear when you stop looking at them. They keep running, processing requests, and exposing data whether your team knows about them or not.
A 2025 industry analysis found that nearly a third of all malicious API transactions targeted unknown or unmanaged endpoints. Not misconfigured APIs. Not poorly authenticated ones. APIs that teams didn't even know existed.
This isn't a visibility problem you can solve with a spreadsheet. It requires purpose-built API discovery tools that can continuously scan, classify, and catalog every endpoint in your environment before an attacker finds the ones you missed.
This guide breaks down the ten best API discovery platforms in 2026, the discovery methods they use, how to evaluate them for your stack, and where the industry is heading next. Whether you're a security lead trying to close blind spots or a platform team building a unified API inventory, this is the breakdown you need.
What Is API Discovery?
API discovery is the systematic process of identifying, cataloging, and classifying every API operating within your organization's infrastructure, including the ones nobody documented. At its core, it answers a deceptively simple question: what APIs do we actually have running right now?
Most organizations can't answer that with confidence. APIs are created during sprints, wired into third-party integrations, deployed for one-off projects, and left running long after the team that built them has moved on. The result is an environment where documented APIs represent only a fraction of what's actually live.
Three categories of problematic APIs make discovery critical:
- Shadow APIs: Endpoints that exist in production but were never formally documented or registered. They operate outside official oversight, meaning security policies, access controls, and monitoring don't apply to them.
- Zombie APIs: Deprecated versions that should have been decommissioned but still accept traffic. They often run on outdated security standards and create duplicate attack surfaces.
- Rogue APIs: Endpoints created without authorization, sometimes by well-meaning developers bypassing slow approval processes, sometimes by malicious actors.
API discovery tools automate the detection of all three categories, turning invisible risk into a manageable, actionable inventory.
Why API Discovery Matters More in 2026 Than Ever Before
API discovery has always been important. But three converging trends have made it urgent.
1. AI-Accelerated API Creation
Developers using AI coding assistants like GitHub Copilot and cursor-based code generators are building APIs faster than ever. An endpoint that used to take a day to scaffold can now be generated in minutes. That speed is valuable, but it creates a documentation and governance gap. APIs are being created faster than teams can register, secure, and monitor them.
When AI agents interact with software systems through APIs, the surface area multiplies further. Every agentic workflow that calls an API becomes a dependency that needs to be tracked.
2. Multi-Gateway and Multi-Cloud Sprawl
Enterprises rarely run a single API gateway anymore. Different teams adopt different platforms: one team on Kong, another on Apigee, a third on AWS API Gateway. Each gateway has its own catalog, its own format, its own blind spots. The result is API sprawl across fragmented management layers where no single team has full visibility.
3. Regulatory Pressure on Data Visibility
Regulations like GDPR, HIPAA, PCI DSS, and PSD2 don't just require you to protect sensitive data; they require you to know where it flows. If an undocumented API is processing PII without proper controls, that's a compliance violation waiting to happen. API discovery is increasingly a prerequisite for API governance and audit readiness.
How API Discovery Tools Actually Work: 4 Core Methods
Not all API discovery tools use the same approach. Understanding the method behind each tool is critical because it determines what the tool can and can't find.
Method 1: Traffic-Based Discovery
How it works: Sensors or agents monitor live network traffic (north-south and east-west) to identify API calls in real time. The tool analyzes request/response patterns to catalog endpoints, parameters, and data flows.
Strengths:
- Finds APIs based on actual production usage
- Detects shadow APIs that receive traffic but aren't documented
- Reveals real-world usage patterns, volumes, and anomalies
Blind spot: If an API hasn't received traffic during the monitoring window, it's invisible. Dormant APIs, seasonal endpoints, and development-only services go undetected.
Tools that use this: Salt Security, Akamai API Security, Wallarm
Method 2: Source Code-Based Discovery
How it works: The tool scans code repositories (GitHub, GitLab, Bitbucket, Azure Repos) to identify API definitions, routes, and endpoints directly from the source code.
Strengths:
- Discovers every API defined in code, including dormant and never-deployed endpoints
- Catches APIs before they reach production
- No dependency on traffic volume or timing
Blind spot: Won't find APIs created outside your code repositories for example, third-party integrations, manually configured gateway routes, or endpoints created by external vendors.
Tools that use this: StackHawk
Method 3: Gateway and Infrastructure-Based Discovery
How it works: Pulls API inventories directly from API gateways, load balancers, service meshes, and cloud infrastructure metadata (like AWS CloudTrail or Azure API Management logs).
Strengths:
- Covers managed APIs that route through official infrastructure
- Low setup overhead integrates with existing platform data
- Strong for environments with centralized gateway management
Blind spot: Only sees what passes through the gateway. Direct service-to-service calls, sidecar proxies, or endpoints that bypass the gateway entirely remain hidden.
Tools that use this: Kong, AWS API Gateway Discovery, Google Apigee
Method 4: Hybrid and Multi-Source Discovery
How it works: Combines two or more methods of traffic analysis, plus code scanning, gateway data, plus runtime behavioral analysis, or external probing plus internal sensor data.
Strengths:
- Broadest coverage compensates for each method's individual blind spots
- Highest confidence in inventory completeness
- Best suited for complex environments with mixed architectures
Trade-off: More integration work upfront, higher cost, and more data to tune and deduplicate.
Tools that use this: Traceable AI, Cequence Security, DigitalAPI
Key Features That Separate Good API Discovery Tools From Great Ones
Every API discovery tool claims to "find all your APIs." The difference is in what happens after discovery. Here's what to evaluate beyond the basics:
1. Automated, Continuous Discovery
One-time scans are snapshots. In environments where APIs are deployed multiple times per day, you need continuous discovery that catches new endpoints within hours, not weeks. The best tools hook into CI/CD pipelines so that newly deployed APIs are discovered at build time.
2. Sensitive Data Classification
Discovery should tell you not just that an API exists, but what data it touches. Tools that automatically flag endpoints handling PII, PHI, payment card data, or financial records give compliance teams the visibility they need without manual reviews.
3. API Ownership and Lifecycle Context
A discovered API without an owner is a liability. The best platforms enrich inventory with metadata: who owns it, when it was last updated, what team deployed it, and where it sits in the API lifecycle from design to retirement.
4. Dependency and Relationship Mapping
APIs rarely operate in isolation. Dependency mapping reveals which services call which endpoints, so teams can assess the blast radius of a change, outage, or security incident. This is especially critical in microservices environments where a single API may be consumed by dozens of upstream services.
5. Risk Scoring and Security Posture
Discovery without a security context is incomplete. Look for tools that score endpoints based on authentication strength, data sensitivity, exposure level, and alignment with the OWASP API Security Top 10.
6. Duplicate and Redundancy Detection
In multi-gateway environments, the same API often exists in multiple catalogs with slightly different names. Intelligent deduplication prevents teams from maintaining redundant endpoints and helps consolidate toward a single source of truth.
7. Integration Depth
Discovery tools must connect to your actual infrastructure: API gateways, CI/CD pipelines, cloud providers, monitoring tools, and security platforms. Without integration, discovery data stays siloed and actionable insights never reach the teams that need them.
Top 10 best API discovery platforms in 2026
1. DigitalAPI API discovery platform

Discovery method: Hybrid (gateway aggregation + AI-powered scanning)
Best for: Enterprises running multiple API gateways who need a unified inventory and full lifecycle control
Most enterprises don't have a discovery problem; they have a fragmentation problem. Different teams use different gateways. Each gateway has its own catalog. APIs get documented in one place, monitored in another, and governed nowhere. Discovery tools that scan a single environment still leave you with a fractured picture.
DigitalAPI.ai solves this by aggregating APIs across every gateway, Kong, Apigee, AWS API Gateway, Azure, MuleSoft, and others into a single unified catalog. Every endpoint gets pulled into one searchable, developer-friendly hub with consistent metadata, regardless of where it was originally deployed.
But discovery is just the starting point. What makes DigitalAPI different is what happens next.
Key capabilities:
- Cross-gateway unification: Automatically pulls APIs from multiple gateways, eliminates duplicates, and enriches entries with consistent metadata. No more hunting across three different dashboards to find one endpoint.
- AI-powered detection: Uses machine learning to detect shadow APIs, flag duplicates, auto-generate OpenAPI documentation, and run OWASP security checks without manual setup.
- Full lifecycle management: Discovery feeds directly into documentation, governance, monitoring, and even monetization. You don't need five separate tools; one platform covers design to retirement.
- Developer portal and marketplace: Discovered APIs are published to a searchable developer portal and marketplace, driving reuse and adoption instead of letting APIs sit undiscovered in a catalog.
- Governance automation: Policies are enforced automatically. Compliance checks, naming conventions, and security standards are baked into the workflow so new APIs are governed from day one.
Pros:
- The only platform that unifies discovery across multiple gateways into a single inventory
- End-to-end lifecycle coverage reduces tool sprawl
- AI automation cuts manual review time significantly
- Developer portal drives API reuse and adoption
Cons:
- The strongest value shows in multi-gateway environments; teams with a single gateway may not need the aggregation layer
- Enterprise-grade features require a demo and custom pricing
Pricing: Custom book a demo for a walkthrough.
2. Salt Security
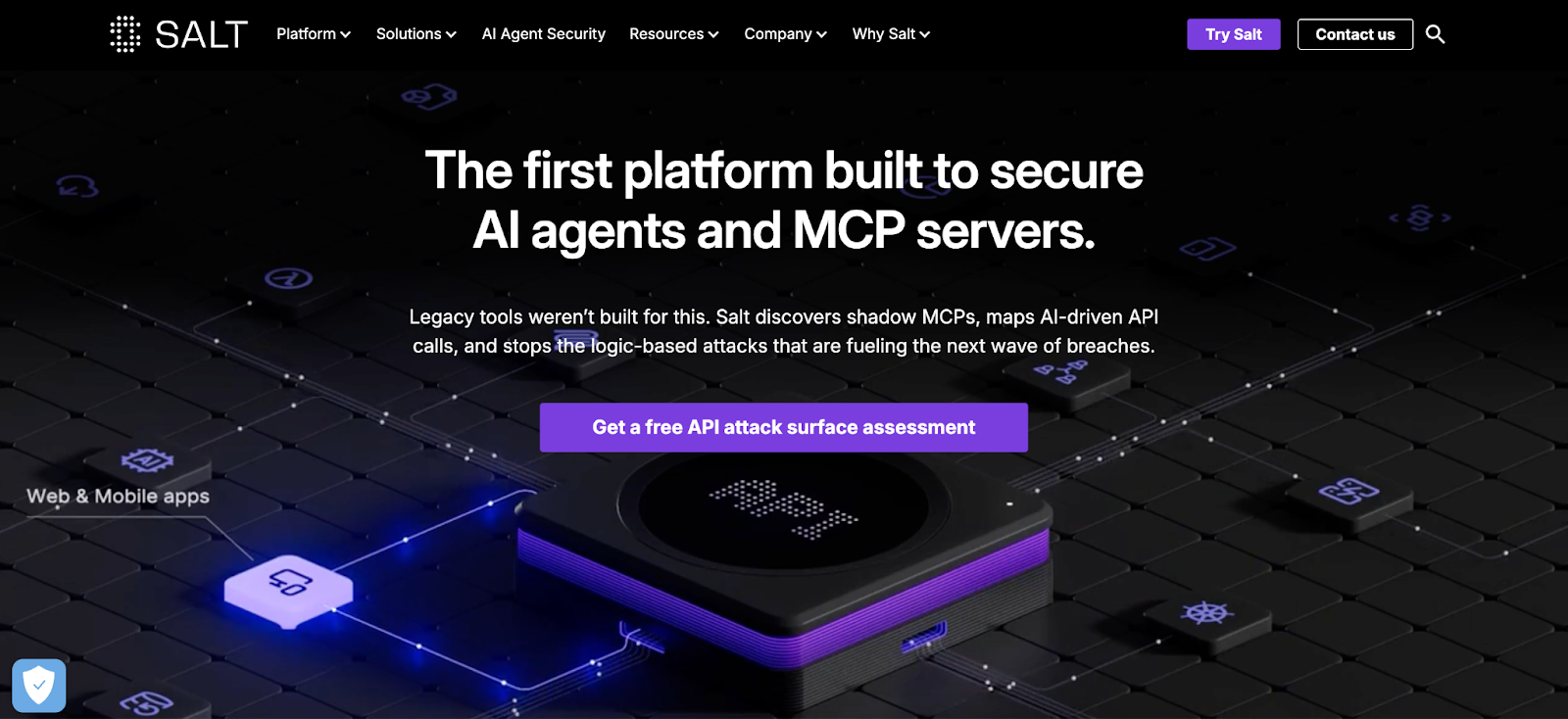
Discovery method: Traffic-based (runtime behavioral analysis)
Best for: Security-first teams that need real-time shadow API detection in large, fast-changing environments
Salt Security monitors live API traffic using out-of-band analysis, meaning it doesn't add latency or modify request flows. It builds a continuously updated inventory by observing what's actually happening in production.
Key capabilities:
- Traffic-driven discovery of known, shadow, and zombie APIs across environments
- Cloud Connect for AWS enables agentless, cloud-native discovery
- The behavioral analytics layer identifies anomalies, abuse patterns, and data exposure risks
- Integrates with major gateways and cloud services for broad deployment coverage
Pros:
- Strong runtime visibility catches shadow APIs that code scans miss
- Behavioral analytics adds security depth beyond simple inventory
- Agentless AWS deployment reduces setup friction
Cons:
- Traffic-dependent: dormant or seasonal APIs that don't receive traffic during monitoring go undetected
- Discovery is security-focused, less suited for teams primarily seeking developer-oriented cataloging
- Enterprise pricing can scale quickly with traffic volume
Pricing: Contact for enterprise pricing.
3. Traceable AI

Discovery method: Hybrid (traffic + gateway + code + eBPF hooks)
Best for: Organizations that want discovery paired with deep analytics for security posture management
Traceable stands out by feeding all discovery data into a proprietary API Data Lake, creating a rich analytical layer where security and ops teams can investigate trends, map dependencies, and understand blast radius.
Key capabilities:
- Multi-source discovery across traffic, gateways, code repositories, and eBPF workload hooks
- Continuous drift monitoring flags undocumented endpoints and schema changes
- Dependency mapping reveals hosting locations, access patterns, and service relationships
- The analytics layer supports trend analysis, investigations, and compliance evidence gathering
Pros:
- Broadest multi-source approach reduces blind spots
- Analytics depth goes beyond inventory into posture management
- eBPF hooks provide kernel-level visibility in containerized environments
Cons:
- Full value requires connecting all data sources, partial deployment limits analytics quality
- Steeper onboarding curve than single-method tools
- Maybe more capability than small teams need
Pricing: Contact for enterprise pricing.
4. Akamai API Security
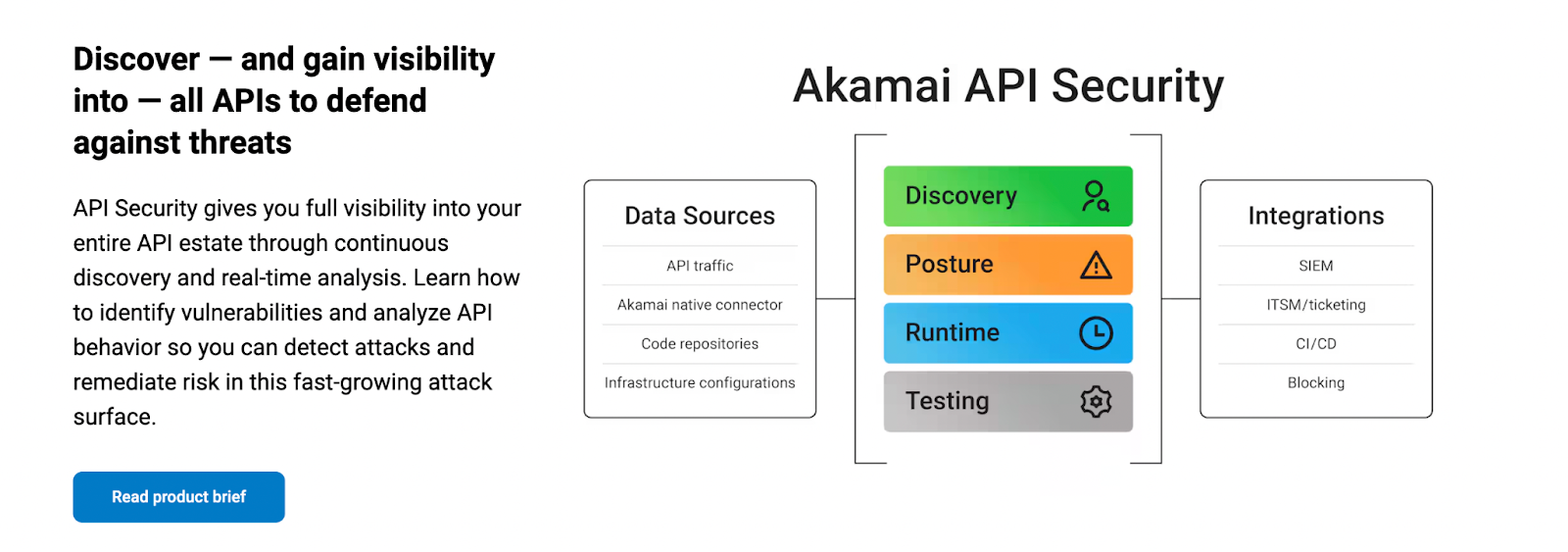
Discovery method: Traffic-based (multi-cloud traffic analysis)
Best for: Enterprises already on Akamai's edge network who want unified API discovery and protection
Akamai's API security platform, bolstered by its 2024 acquisition of Noname Security, provides traffic-based discovery that integrates tightly with Akamai's existing CDN, WAF, bot defense, and DDoS protection stack.
Key capabilities:
- Continuous traffic-based discovery of shadow, zombie, and rogue APIs across cloud environments
- Protocol support spanning REST, GraphQL, SOAP, XML-RPC, and JSON-RPC
- Automated sensitive data classification (PII, financial data, IP)
- Tight integration with Akamai WAAP, bot management, and edge security products
Pros:
- Natural fit for organizations standardized on Akamai's security stack
- Broad protocol coverage catches non-REST APIs that other tools miss
- Edge-level integration means discovery data feeds directly into protection policies
Cons:
- Strongest when deployed within Akamai's ecosystem, less compelling as a standalone tool
- Traffic-dependent: shares the same dormant-API blind spot as other traffic-based tools
- Integration benefits diminish if you're not already on Akamai's CDN
Pricing: Contact Akamai for enterprise pricing.
5. Cequence Security
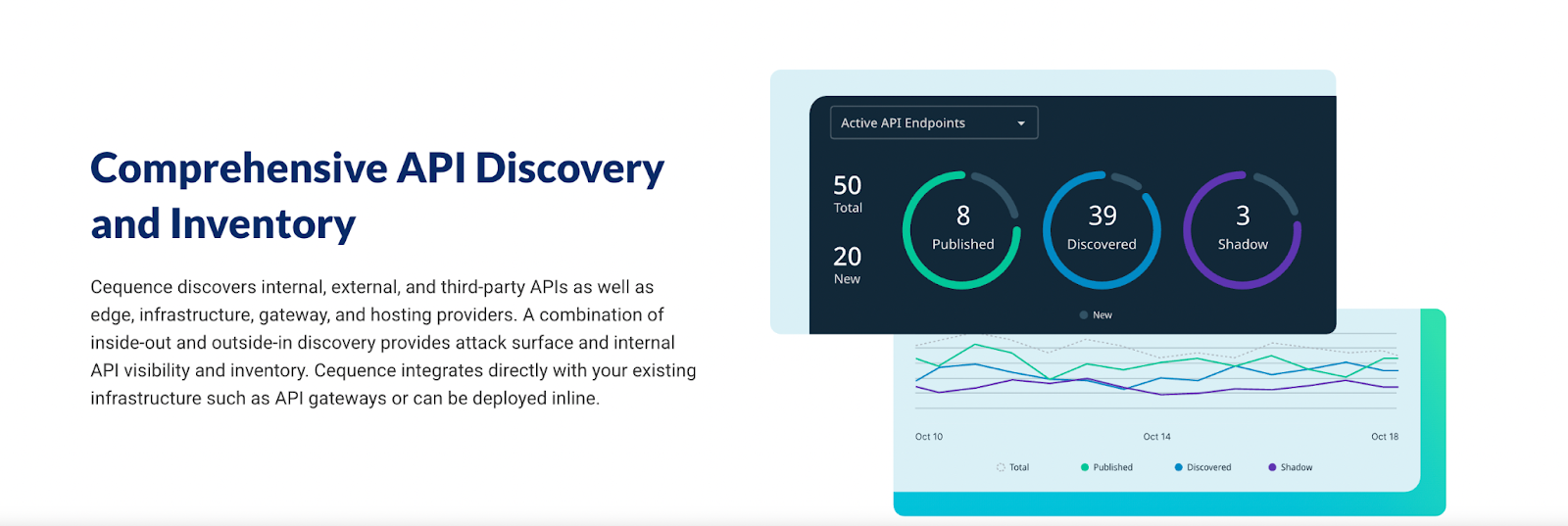
Discovery method: Hybrid (outside-in external scanning + inside-out internal sensors)
Best for: Organizations that need an attacker's-eye view of their API exposure alongside internal inventory
Cequence offers a distinctive dual-lens approach. Its external scanning maps publicly accessible APIs the way an attacker would find them, while internal sensors cover private, service-to-service endpoints. Merging both views produces a unified inventory with both internal and external visibility.
Key capabilities:
- Outside-in scanning surfaces public APIs you may not realize are exposed
- Internal integrations and sensors cover private endpoints and service-to-service communication
- Unified inventory merges external and internal findings for complete coverage
- Lightweight deployment without deep instrumentation requirements
Pros:
- Attacker's-eye view reveals exposure that internal-only tools miss
- The dual-lens approach provides both offensive and defensive visibility
- Lightweight setup compared to traffic-analysis platforms
Cons:
- External scanning depth depends on target accessibility; heavily firewalled environments may limit outside-in results
- Less analytics depth compared to dedicated data-lake approaches like Traceable
- Internal coverage still benefits from complementary traffic or code-based tools
Pricing: Contact for enterprise pricing.
6. Imperva API Security
Discovery method: Traffic-based (continuous discovery with automated risk classification)
Best for: Teams that want a straightforward discover-and-classify workflow feeding into WAF and bot protection
Imperva focuses on combining continuous discovery with immediate risk classification, so every discovered endpoint comes with a security verdict rather than just a catalog entry.
Key capabilities:
- Continuous shadow API discovery across environments with automated change tracking
- Automated risk classification flags OWASP API Top 10 vulnerabilities and design flaws
- Sensitive data endpoint identification helps prioritize compliance-critical APIs
- Protection against BOLA and BOFLA attacks through behavioral monitoring
- Deep integration with Imperva's WAF, bot management, and DDoS protection suite
Pros:
- Risk classification is automated and immediate, with no manual triage needed
- Strong for organizations already using Imperva's broader security stack
- BOLA/BOFLA detection adds depth beyond basic vulnerability scanning
Cons:
- Deepest value is within Imperva's ecosystem, where standalone users may find integration limitations
- Less focus on developer-facing features like portals or documentation
- Traffic-dependent discovery shares standard blind spots
Pricing: Contact Imperva for enterprise pricing.
7. Palo Alto Networks Prisma Cloud

Discovery method: Infrastructure-based (cloud workload and service analysis)
Best for: Cloud-first organizations using Palo Alto's CNAPP stack who want API discovery woven into cloud security posture management
Prisma Cloud treats API discovery as a native feature of cloud security, not a bolted-on capability. It discovers APIs within the context of cloud workloads, identities, and exposure paths.
Key capabilities:
- Discovers APIs across cloud workloads, serverless functions, and container services
- Maps risks in context with vulnerabilities, identities, and exposure paths
- Attack-path visualization helps prioritize which risks to remediate first
- Unified view across cloud security posture, workload protection, and API inventory
Pros:
- API discovery enriched with cloud context (IAM, network exposure, workload vulnerabilities)
- Attack-path views provide actionable prioritization
- Strong for teams already in the Palo Alto CNAPP ecosystem
Cons:
- Strongest for cloud-native environments, on-prem or hybrid APIs may have limited coverage
- API discovery is one module within a broader platform, not a standalone product
- Pricing is tied to the broader Prisma Cloud license
Pricing: Contact Palo Alto Networks for enterprise pricing.
8. Microsoft Defender for APIs

Discovery method: Infrastructure-based (Azure-native service analysis)
Best for: Azure-first organizations that want low-friction API discovery integrated into their existing Microsoft security stack
For teams running on Azure, Defender for APIs provides native discovery and monitoring without additional agents or third-party integrations.
Key capabilities:
- Continuous discovery across Azure API Management, Logic Apps, and Function Apps
- Unified inventory with security recommendations and real-time alerts
- Seamless integration with Defender for Cloud and Microsoft Sentinel SIEM
- Risk assessment based on data sensitivity, authentication, and exposure
Pros:
- Zero-friction setup for Azure environments, no additional agents needed
- Deep integration with Microsoft's broader security ecosystem
- Security recommendations are context-aware and actionable
Cons:
- Azure-only: doesn't discover APIs on AWS, GCP, or on-prem infrastructure
- Onboarding can increase load on Azure API Management instances. Microsoft recommends a gradual rollout
- Limited value for multi-cloud organizations unless paired with another tool
Pricing: Included with Microsoft Defender for Cloud plans.
9. Google Apigee
Discovery method: Gateway-based (API Hub cataloging + Shadow API Discovery)
Best for: Google Cloud customers who need API cataloging with shadow API detection integrated into their existing gateway
Apigee combines its API Hub for centralized cataloging with a dedicated Shadow API Discovery that analyzes traffic to find undocumented endpoints.
Key capabilities:
- Observation jobs analyze traffic patterns and reconcile findings against known inventory
- Shadow discovery results are centralized into the API Hub for unified cataloging
- The Advanced API Security module adds anomaly and abuse detection
- AI-powered tools support lifecycle management and documentation accuracy
Pros:
- Native integration with Google Cloud services
- API Hub provides a strong cataloging foundation
- Shadow API discovery adds security value on top of standard gateway management
Cons:
- Most compelling within the Google Cloud ecosystem, less relevant for AWS or Azure-primary organizations
- Discovery capabilities are gateway-centric APIs that bypass Apigee go undetected
- Advanced security features require additional licensing beyond the base Apigee
Pricing: Part of Google Cloud's API management pricing. Contact Google for enterprise details.
10. Postman

Discovery method: Traffic-based (Insights Agent)
Best for: Developer-centric teams who want discovery embedded in the tools they already use for testing, documentation, and collaboration
Postman's approach is unique: instead of building another security-focused scanner, it embeds discovery directly into the developer workflow where APIs are built and tested.
Key capabilities:
- Postman Insights Agent observes traffic and automatically surfaces endpoints per service
- Endpoints view lets teams validate, merge, and refine discovered endpoints with human-in-the-loop accuracy
- Integrates with Postman's Private API Network for cataloging, reuse, and documentation
- Discovery connects directly with testing, monitoring, mocking, and documentation features
Pros:
- Embedded in the tool developers already use, the lowest adoption friction
- Human-in-the-loop validation improves discovery accuracy over time
- Discovery feeds directly into testing and documentation workflows
Cons:
- Security features are lighter compared to dedicated API security platforms
- Traffic-based: shares dormant-API blind spots with other traffic-based tools
- Best suited as a development-side discovery tool, security teams may need a complementary platform
Pricing: Free tier available. Paid plans for teams and enterprise start at $14/user/month.
How to Choose the Right API Discovery Platform: A Decision Framework
Picking an API discovery tool isn't just a technical decision; it's a strategic one that affects your security posture, compliance readiness, and developer velocity. Here's a structured framework for evaluating options:
Step 1: Map Your API Landscape Complexity
Start with an honest assessment:
- How many gateways do you run? If the answer is more than one, you need a tool that aggregates across gateways (like DigitalAPI) rather than one that sees only a single environment.
- What's your cloud footprint? Single-cloud teams can leverage native tools (Defender for Azure, Apigee for GCP). Multi-cloud environments need platform-agnostic discovery.
- How fast are APIs being created? High-velocity development teams (especially those using AI coding tools) need continuous discovery, not periodic scans.
Step 2: Define Your Primary Use Case
Different tools optimize for different outcomes:
Step 3: Evaluate Integration Depth
API discovery doesn't happen in isolation. The tool must connect with:
- Your API gateways (single or multi-gateway setups)
- CI/CD pipelines for shift-left discovery
- SIEM and security tools for incident response
- Monitoring and analytics platforms for operational visibility
Step 4: Assess Total Cost of Ownership
Look beyond sticker price:
- Per-API vs. per-traffic-volume vs. flat licensing
- Infrastructure requirements (agents, sensors, cloud resources)
- Integration and onboarding costs
- Training time for security and development teams
- Ongoing tuning to reduce false positives
For a deeper dive on API infrastructure spending, see our guide on API cost control and optimization.
Step 5: Run a Proof of Concept
Never buy based on demos alone. Deploy the tool in a representative slice of your environment and measure:
- Discovery completeness: Did it find APIs you already knew about? Did it find ones you didn't?
- False positive rate: How much noise did it generate?
- Time to value: How quickly did actionable insights appear?
- Integration friction: How much custom work was needed to connect to your stack?
The Future of API Discovery: What's Changing in 2026 and Beyond
API discovery isn't a static category. Several trends are reshaping what these tools need to do:
AI-Native Discovery
Discovery tools are increasingly using machine learning not just to find APIs, but to classify them, predict risk, detect behavioral anomalies, and auto-generate documentation. As AI reshapes API governance, expect discovery to become the data layer that feeds AI-driven security and compliance automation.
Discovery for AI Agent APIs
As AI agents increasingly interact with systems through APIs (via protocols like MCP), discovery tools need to track not just human-consumed APIs but machine-to-machine agent endpoints. Managing AI agent permissions starts with knowing which APIs agents can access.
Shift-Left Discovery
The trend is moving discovery earlier in the development lifecycle into code repositories, pull requests, and CI/CD pipelines. Instead of discovering APIs after they hit production, teams catch them at build time and apply governance policies before deployment.
Discovery as the Foundation of API Marketplaces
Organizations are realizing that discovery isn't just a security tool, it's the first step toward building an internal API marketplace where developers can find, evaluate, and reuse existing APIs instead of building from scratch. Discovery drives reuse. Reuse drives efficiency. Efficiency drives ROI.
Challenges and Limitations to Expect
No API discovery platform is perfect. Being aware of common limitations helps set realistic expectations:
- False positives in automated scanning: Tools may flag non-API endpoints or surface duplicate results. Teams need processes to triage and validate findings without burning bandwidth on noise.
- Integration overhead: Discovery platforms need to connect with gateways, CI/CD pipelines, cloud providers, and monitoring tools. Setting up these integrations takes time and cross-team coordination.
- Dormant API blind spots: Traffic-based tools can't find what isn't being called. Code-based tools can't find what isn't in your repositories. No single method catches everything, which is why hybrid approaches exist.
- Cost at scale: Enterprise-grade discovery platforms carry significant licensing, infrastructure, and operational costs. Evaluate the total cost of ownership carefully before committing.
- Skill requirements: Discovery generates data, but data alone doesn't solve problems. Teams still need the expertise to interpret findings, connect them to governance workflows, and act on risks.
Frequently Asked Questions
1. What is an API discovery tool?
An API discovery tool automatically identifies, catalogs, and classifies every API in your infrastructure, including shadow, zombie, and rogue APIs that aren't formally documented. It provides a continuously updated inventory that feeds into security, governance, and compliance workflows.
2. What is the best API discovery tool in 2026?
The best tool depends on your environment. For multi-gateway enterprises, DigitalAPI provides the broadest unification. For security-first teams, Salt Security and Traceable AI offer deep runtime analytics. For Azure-native shops, Microsoft Defender for APIs is the lowest-friction option. For developer-centric teams, Postman embeds discovery directly into existing workflows.
3. How do API discovery tools detect shadow APIs?
Different tools use different methods: traffic analysis identifies undocumented endpoints that are actively receiving requests. Source code scanning finds endpoints defined in code but never registered. External scanning probes your perimeter the way an attacker would. The most comprehensive tools combine multiple methods for maximum coverage.
4. What is the difference between API discovery and API management?
API discovery is the process of finding and cataloging APIs. API management is the broader discipline of controlling APIs throughout their lifecycle from design and documentation to security, monitoring, rate limiting, and retirement. Discovery is the first step; management is the ongoing practice.
5. Are API discovery platforms necessary for small businesses?
Yes. Even a few undocumented APIs can create security vulnerabilities or compliance gaps. Small businesses may not need enterprise-scale platforms, but lightweight discovery tools (like Postman's built-in features or gateway-native capabilities) provide essential visibility at minimal cost.
6. How does AI improve API discovery?
AI enhances discovery by analyzing large volumes of traffic and code to detect patterns humans would miss. It automates sensitive data classification, generates API documentation, detects behavioral anomalies, and reduces false positives through machine learning, making discovery faster, more accurate, and more actionable.
7. Can API discovery help with regulatory compliance?
Absolutely. Discovery tools identify which endpoints handle sensitive data (PII, PHI, financial records), map data flows, and generate audit trails. This visibility is essential for demonstrating compliance with GDPR, HIPAA, PCI DSS, PSD2, and SOC 2 especially during audits where regulators expect documented evidence of data handling practices.
8. What is the difference between API discovery tools and API discovery platforms?
An API discovery tool typically focuses on a single function: finding APIs in your environment. An API discovery platform extends beyond detection to include lifecycle management, governance, documentation, security, and developer enablement. Tools solve the visibility problem; platforms solve the management problem that visibility reveals.
You’ve spent years battling your API problem. Give us 60 minutes to show you the solution.
.svg)

%20(1).png)




.avif)
